Many schools and nurseries in the UK partner with external companies to “fundraise” around Christmas, offering your child’s art printed on cards, mugs, etc. The school gets 20% of the item cost back and parents get a lovely keepsake. My daughter’s nursery did this for this Christmas. They had all their children do little Christmas-themed things, including many hand and foot prints.
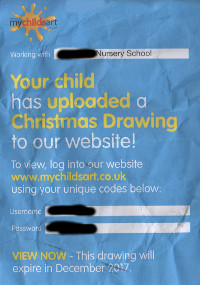
In our case, they sent the physical prints off to a company called Crestline Printers Limited, trading as My Child’s Art. Crestline scanned them all in provided the nursery with leaflets to distribute to parents. These leaflets (right) contain a school-wide username and password. Holders of this leaflet can log in (without an encrypted connection), pick their child out of a list of everybody at that school, and then decide whether or not to have their art printed on a range of stuff.
While that all sounds nice enough, there are systemic failures here that mean literally anyone can harvest identifiable data and fingerprints from children.
No SSL certificate means no security.
Seriously, if you run a website, get a SSL certificate and use it, everywhere.
Without encryption, the traffic between you and your users is forfeit. A bad actor on the network can inject and (here) intercept login details. It just takes one parent (and there must be at least 300 at my nursery) to log in at a cafe, or a dodgy access point, and my daughter’s data is compromised.
Certificates aren’t expensive. Let’s Encrypt is free (and good). Others are cheap. They’re not hard to configure. They open the door to transport protocols like HTTP/2 which are faster. Google prefers encrypted sites in search results. Not to mention that modern browsers kick up a ton of warnings if you try to log in without encryption.
It’s entirely likely that credentials for at least one school accounts Crestline manages has had their details leaked out to complete strangers by this lack of basic security.
The positives make this a no-brainer for any site but I really struggle to comprehend how a site that handles data for thousands of children was deployed without this. It calls a lot of the other security into question. Get a bloody certificate and use it.
Don’t hand out a register of full names to anybody who logs in
This is sketchy at best, a data protection issue at worst. I’m sure this data is probably available elsewhere but really, this is what made me stop and start asking questions.
This is easy to fix too. I know my daughter’s name! I should have to enter that in to see her work.
You can see as many children’s art as you like
It’s just a checkbox system on the current list. You can select as many as you like, even run $('.letter_group input').trigger('click') in a console to tick them all. And it lets you view them all.
The system shouldn’t let you do this. It’s silly. Selecting 173 children should raise alarms.
You can see high-resolution scans for all children.
Once you’ve selected all the children, you’re shown every bit of art in a big long list. Right click one and select “View background image” and you get a 7Mpx version. Enough detail to make out fingerprints in good transfers.
Fingerprints don’t change much as people grow up. They get bigger but the patterns largely remain within extracted patterns. One captured today could be used to trick a scanner in 10 years time.
Thankfully there were only a few usable prints on the system… But I shouldn’t have to rely on it being hard to [inadvertently] fingerprint children to protect their biometrics. What if they decide to do Easter retinal scans or Hanukkah voice prints?
There’s also a copyright angle here. If my child paints the Mona Lisa of Christmas trees, anybody can order it (without permission). If she becomes stupidly famous, this art, her fingerprints, all the other rubbish that’s being warehoused about everybody… Gains value amongst bad people.
But the worst thing here is something that any service providers should understand…
Nurseries and schools aren’t are security experts
You’ve given the schools a “secure” username and password so they think they and their children are safe. Job done, 20% kickback, easy money. But this just highlights a recurring theme in security: users are idiots. They only consider what they know and most of them know very little in this respect. They’re educators, not developers.
This is highlighted by the plethora of MCA logins available through simple searches on Google. Schools want to share this stuff (for the cash) but don’t appreciate they’re leaking all their kids’ details and biometrics in the process.
Crestline needs to improve their system to offset the complacency of schools. I’ve invited them to fix this mess, and comment. If you know of other systems like this, please let me know in the comments.